Protocols are defined as the set of rules and procedures used for transmitting the information and data between electronic devices including computers. Similarly, the VPN protocols are also regarded as the set of rules or instructions that are used for determining the process of data being routing between the computer and the VPN server. VPN providers every time rely on VPN protocols in ensuring to build a secure and stable connection in-between the devices.
What is VPN?
VPN is regarded as the Virtual Private Network that works to hide the online activities being conducted by the users and also in encrypting the traffic like hackers, intruders, and third parties by preventing their penetration to the users’ device. In short, VPN is regarded as the Virtual Private Network needed for building a secure and private network connection over the public and unsecured public internet connection.
Read More >>>> How to Configure Linksys Router?
Why VPN protocols are important?
Here we can conclude that the VPN Protocols are used for determining the facts that how data is transmitted and routed between the device connection. Every VP Protocols are based on specified specialization and thus, based on these specifications the VPN Protocols are beneficial in offering desired benefit and circumstances.
In this article, we are detailing the different types of VPN protocols along with the powerful benefits that the users may attain on using these protocols for data transmission. Many people also use VPNs for unblocking streaming platforms such as amazon prime, Netflix, Hulu, Kodi, etc. Here, these VPNs protocols play an important role. You can also refer to these best free VPNs for kodi. Though for grabbing more entertainments stuff on Kodi you need to unblock its addons and by using a VPN you can unlock it here are the best Kodi addons.
Types of VPN Protocols
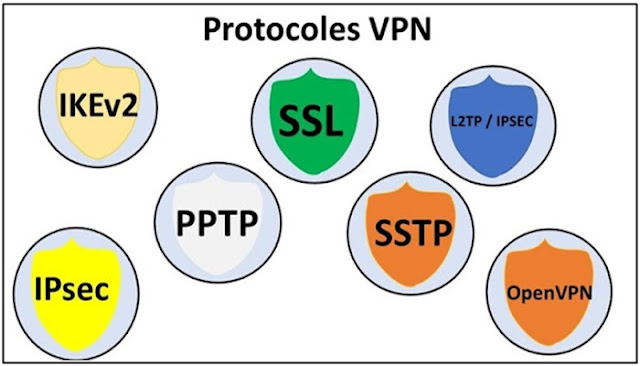
The VPN Protocols are classified based on their functionality and these approaches are as follows:
a. Two protocols (one for moving the data through the tunnel and the second for securing the traffic)
b. One protocol (single protocol for transferring data and data security)
Here is the list of the VPN protocols that are highly used by the users for fulfilling the purpose of transmission of data and information between the electronic devices. The VPN Protocols are as follows:
1. PPTP:
PPTP refers to the Point-to-Point Tunneling Protocol and is regarded as one of the oldest VPN Protocols that has been designed during the mid of 90s by Microsoft and PPTP was known for its integration within Windows 95 and is specially designed for dialing the connections.
PPTP i.e. Point-to-Point Tunneling Protocol lacks security features but was known for its advanced technology and basic encryption feature. Apart from these, PPTP VPN Protocol is also considered as the best protocol for its best connection speed to the users willing to prevent heavy encryption. Some of the advanced features of this VPN Protocol include faster data speeds, widely support, many security issues, and many more.
2. L2TP/ IPSec:
L2TP is considered as the replacement of PPTP VPN Protocol and it stands for Layer 2 Tunnel Protocol that in general was frequently paired with the security protocol IPSec. The protocol is not a perfect protocol for offering new techniques of encryption or privacy out-of-the-box. Layer 2 Tunneling Protocol when paired with the Security Protocol IPsec tends to offer the extreme security feature and has no vulnerabilities. Some of the additional and advanced features of this L2TP/ IPsec include effective speed, used on a wider scale, easily blocked because of reliance of UDP on the single port.
Read More >>>> UDP Vs TCP
3. OpenVPN:
OpenVPN refers to the open-source protocol that ensures that the developers could easily access the underlying code and this protocol is known for its AES-256 bit key encryption using the 2048-bit RSA authentication and 160-bit SHA1 hash algorithm. The additional features of the OpenVPN protocol include open source in nature, have the strongest encryption, and offer slower speeds.
4. SSTP:
SSTP stands for Secure Socket Tunneling Protocol and the reason for its popularity is its full integration with every Operating System designed by Microsoft like Windows Vista SP 1. SSTP or Secure Socket Tunneling Protocol is executable on the concept of 2048-bit SSL/ TLS certification for fulfilling the purpose of authentication and 256-bit SSL keys for encryption. The additional features of this VPN Protocol i.e. SSTP include good security, great support for native and third-party clients, and difficulty to block and detect.
5. IKEv2:
IKEv2 defines the Internet Key Exchange version 2, a common VPN tunneling protocol that offers a secure key exchange session. Like the L2TP and IKEv1, IKEv2 is also paired with the security protocol i.e. IPSec for encryption and authentication. The exclusive features of the IKEv2 VPN Protocol are as follows:
a. Fast and mobile-friendly VPN Protocol
b. Network switching capabilities
c. Open source option
d. Great support for native and third-party clients.
6. Internet Protocol Security (IPSec):
Internet Protocol Security usually abbreviated as IPSec is usually used for Securing Internet Communication across the IP Network. IPSec helps in securing the Internet Protocol Communication by verifying the session and helps in encrypting data packets during the connection. IPSec executes in two modes and they are as follows:
a. Transport mode is used for encrypting the message in the data packet.
b. Tunneling mode is used for encrypting the whole data packet.
7. Secure Shell (SSH):
SSH or Secure Shell helps in generating the VPN tunnel through which the data transfer occurs ensuring that the tunnel is encrypted. SSH connection generated through SSH client and data is transferred from a local port on to the remote server via an encrypted tunnel.
Conclusion:
The aforementioned article signifies the list of VPN protocols defining their primary usage as the protocol in transferring the data by encrypting the data packet. VPN Protocol specifies the set of rules used for determining the facts of how data is transmitted and routed between the device connection. Also, if you are looking for a VPN that has all these protocols measures you can use Surfshark VPN.
No comments:
Post a Comment